Ticketweb followup
Ticketweb (a UK arm of Ticketmaster) have confirmed that someone was able to send emails to subscribers fraudulently. Their initial response was covered on the Naked Security blog.
A second email was sent out this evening:
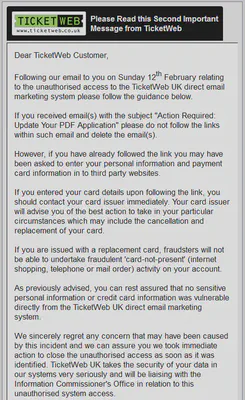
One part which stands out says:
We sincerely regret any concern that may have been caused by this incident and we can assure you we took immediate action to close the unauthorised access as soon as it was identified.
This isn’t quite true, Ticketmaster’s own webserver still issues redirects to people who click on the original link. (Note: I don’t recommend you do this unless you are aware of the potential consequences!)
$ curl -D - "http://smr.mm.ticketmaster.com/track?type=click&enid=ZWFzPTEmbWFpbGluZ2lkPTE0MTQzNjMmbWVzc2FnZWlkPTE0NDU0MjMmZGF0YWJhc2VpZD1EQVRBQkFTRUlEJnNlcmlhbD0xNjgxNzIzMyZlbWFpbGlkPWRhdmlkQGVkZWNhLm5ldCZ1c2VyaWQ9NTM3NzYyMzE3JmZsPSZleHRyYT1NdWx0aXZhcmlhdGVJZD0mJiZodHRwOi8vd3d3LjIwMTItYWNyb2JhdC1hZG9iZS1kb3dubG9hZC5jb20v"
HTTP/1.1 302 Found
Date: Mon, 13 Feb 2012 23:46:55 GMT
Server: Apache/2.2.3 (Unix)
set-cookie: CAMEFROM=NTFMM1414363_1445423[click; domain=.ticketmaster.com; path=/;
Location: http://www.2012-acrobat-adobe-download.com/
Content-Length: 0
Connection: close
Content-Type: text/html
This 302 redirect instructs your browser to go to the URL in the Location header, which is still set to www.2012-acrobat-adobe-download.com.
The domain name was registered through Regtime Ltd., who pop up on sites including:
- The Zeus Tracker
- A “Spotting the bad guys” page from 2009
- The SpyEye Tracker
- Numerous other spam trackers
There is still a valid A record giving the IP address 121.11.80.161 but there is currently no HTTP service running on port 80. This suggests that even though the site is currently down the bad guys behind it probably still have access to their own DNS.
Other articles
By now this has been covered extensively including at ZDNet (Hackers compromise Ticketweb email system) and The Register (“TicketWeb coughs to email database hack”).
Final thoughts
It is good that Ticketweb have taken this seriously and have issued some sensible advice. This is a responsible way of handling any sort of security incident.
However it would be great to see the original links killed so that there is no possible chance of anybody else falling foul to the emails from this point onwards.