Stupid password rules
Today I forgot the password for a site I use only occasionally. This is rare, as I have a number of password schemes that I use to create a password unique to each site. After clicking the reset password link, I am confronted with the “password strength checker” below:
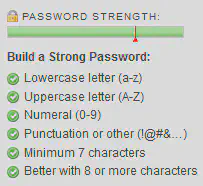
This list of rules doesn’t fit very well with my password scheme, primarily because what I computed in my head fails the test for uppercase characters.
Using the phrase this is an unbelievably long password that would take a very long time to crack fails this rule too, as well as the tests for a number and punctuation. I’m not suggesting that this is a good password, but it’s certainly better than aA1!bcde which passes all the rules. These 8 characters are trivial to brute force on any modern machine even if the underlying software uses a salted hash.
The offending software appears to be Jive, who perhaps need to set some more sensible defaults on their login system.